Overview:
Port security can be used on an interface to identify and limit the MAC addresses of clients that are allowed to access that port.
Solved: Good morning every body:-) i need your help; i activated the port security in my packet tracer, and now this is what i have: Switch#show port-security int fast 0/3 Port Security: Enabled Port Status: Secure-up Violation Mode: Shutdown. Switch(config-if)#switchport port-security maxi Switch(config-if)#switchport port-security maximum 1 Switch(config-if)#switchport port-security viol Switch(config-if)#switchport port-security violation sh Switch(config-if)#^Z Switch#%SYS-5-CONFIGI: Configured from console by console Switch#sh por Switch#sh port-security interfa Switch#sh port. Packet Tracer Activity 2.2.4.10: Troubleshooting Switch Port Security. The employee who normally uses PC1 brought his laptop from home, disconnected PC1, and connected the laptop to the telecommunication outlet. After reminding him of the security policy that does not allow personal devices on the network, you now must reconnect PC1 and re. Switch#show port-security address Switch#show port-security address interface f0/1 Switch#show interface status err-disabled PacketTracer Lab: CCNA-6.1-Configure-verify-and-troubleshoot-port-security.pkt. Subscribe Now for access to the labs!
Study Notes:
- Port security identifies the MAC addresses of clients allowed to forward traffic through an interface
- Port security is applied to access ports
- Port security cannot be applied to a trunk port
- Port security cannot be applied to the destination port for a SPAN port
- Port security cannot be applied to an EtherChannel/Port-Channel interface
- Port security and static MAC configuration are mutually exclusive
- By default
- Port security is turned off
- The maximum number of secure MAC addresses is 1
- When a violation occurs the port gets shutdown
- Aging is disabled
- Aging type is absolute
- Static aging is disabled
- Sticky is disabled
- If the number of MAC addresses configured on a port is less than the maximum then the remaining MAC addresses are able to be learned dynamically
- If a port shuts down, all dynamically learned MAC addresses are removed
- A sticky MAC lets an interface retain dynamically learned MAC addresses when the switch is restarted or if the interface goes down and is brought back online
- To recover a port from err-disabled, you must shut and no shut it
- Port-security violation modes:
| protect | Drops all the packets from the insecure hosts at the port-security process level but does not increment the security-violation count |
| restrict | Drops all the packets from the insecure hosts at the port-security process level and increments the security-violation count |
| shutdown | Shuts down the port if there is a security violation |
Required
Optional
6.1.a Static/6.1.b Dynamic
Set the MAC addresses that are allowed to use the port. If less than the maximum are set than the remaining are learned dynamically.
6.1.c Sticky
Enable sticky learning on the interface
6.1.d Maximum MAC Addresses
Set the number of MAC addresses allowed to use this port
6.1.e Violation Actions
Set the action to be taken when port-security is violated
6.1.f Err-disabled recovery
Once port security is violated on an interface, the interface will go to err-disabled. To return it to normal, do the following:
Verification commands
PacketTracer Lab:CCNA-6.1-Configure-verify-and-troubleshoot-port-security.pkt
Port security is a layer two traffic control feature on Cisco Catalyst switches. It enables an administrator configure individual switch ports to allow only a specified number of source MAC addresses ingressing the port. Its primary use is to deter the addition by users of 'dumb' switches to illegally extend the reach of the network (e.g. so that two or three users can share a single access port). The addition of unmanaged devices complicates troubleshooting by administrators and is best avoided.
Enabling Port Security
Port security can be enabled with default parameters by issuing a single command on an interface:
Although only a single interface is used for illustration in this article, port security, if configured, is typically configured on all user-facing interfaces.
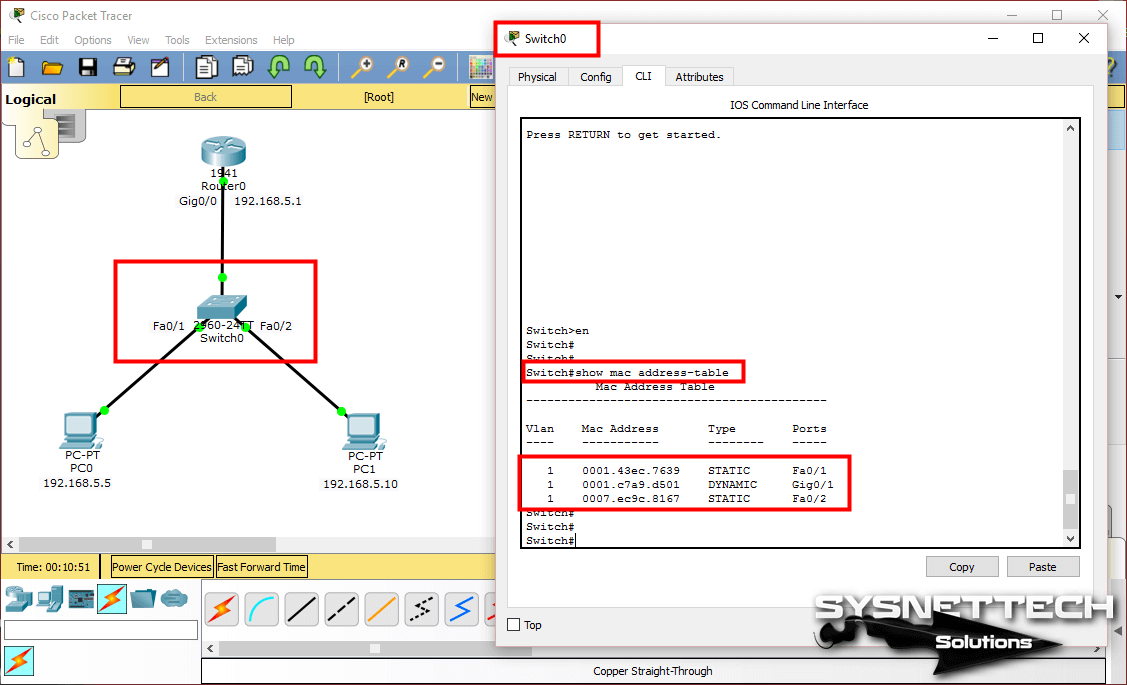
We can view the default port security configuration with show port-security:
As you can see, there are a number of attributes which can be adjusted. We'll cover these in a moment.When a host connects to the switch port, the port learns the host's MAC address as the first frame is received:
Now, we disconnect the host from the port, connect a small switch or hub, and reconnect the original host plus a second, unauthorized host so that they both attempt to share the access port. Observe what happens as soon as the second host attempts to send traffic:
Inspecting the status of port security on the port again, we can see that the new MAC address triggered a violation:
Packet Tracer 7.2.2.4 Answers
By default, a port security violation forces the interface into the error-disabled state. An administrator must re-enable the port manually by issuing the shutdown interface command followed by no shutdown. This must be done after the offending host has been removed, or the violation will be triggered again as soon as the second host sends another frame.
Tweaking Port Security
Violation Mode
Port security can be configured to take one of three actions upon detecting a violation:
shutdown (default); The interface is placed into the error-disabled state, blocking all traffic.protect; Frames from MAC addresses other than the allowed addresses are dropped; traffic from allowed addresses is permitted to pass normally.restrict; Like protect mode, but generates a syslog message and increases the violation counter.
By changing the violation mode to restrict, we are still alerted when a violation occurs, but legitimate traffic remains unaffected:
Unfortunately, violating traffic will continue to trigger log notifications, and the violation counter will continue to increase, until the violating host is dealt with.
Maximum MAC Addresses
By default, port security limits the ingress MAC address count to one. This can be modified, for example, to accommodate both a host and an IP phone connected in series on a switch port:
One also has the option to set a maximum MAC count for the access and voice VLANs independently (assuming a voice VLAN has been configured on the interface):
MAC Address Learning
An administrator has the option of statically configuring allowed MAC addresses per interface. MAC addresses can optionally be configured per VLAN (access or voice).
The configured MAC address(es) are recorded in the running configuration:
Obviously, this is not a scalable practice. A much more convenient alternative is to enable 'sticky' MAC address learning; MAC addresses will be dynamically learned until the maximum limit for the interface is reached.
After a MAC address has been learned, it is recorded to the configuration similarly to as if it were entered manually:
MAC Address Aging
By default, secure MAC addresses are learned (in effect) permanently. Aging can be configured so that the addresses expire after a certain amount of time has passed. This allows a new host to take the place of one which has been removed. Aging can be configured to take effect at regular intervals, or only during periods of inactivity. The following example configures expiration of MAC addresses after five minutes of inactivity:
After five minutes of inactivity, we can see that the address has been purged:
At this point, the old address will be re-learned the next time a frame is sent from that host, or a new host can take its place.
Auto-recovery
To avoid having to manually intervene every time a port-security violation forces an interface into the error-disabled state, one can enable auto-recovery for port security violations. A recovery interval is configured in seconds.
Ten minutes after a port was error-disabled, we can see that the port is automatically transitioned back into operation:
This is a great way to automatically clear port security violations after the user has been given an opportunity to remove the offending host(s). Note that is the cause is not cleared, the violation will trigger again after the port comes back up, re-initating the auto-recovery cycle.
5.3.2.8 Packet Tracer
Footnote
8.2.2.7 Packet Tracer Answers
Although a deterrent, port security is not a reliable security feature, as MAC addresses are trivially spoofed, and multiple hosts can still easily be hidden behind a small router. IEEE 802.1X is a much more robust access edge security solution.